In a recent blog post, CCP Falcon outlined CCP’s response to the hardware vulnerabilities presented as code name Spectre and Meltdown. I work in a couple of IT support teams, and as such I too have been very busy with patching these vulnerabilities. As such, I thought I would take a moment or five to break out what these vulnerabilities are, what your response should be, and what to expect from the patches.
The TL;DR Version of this Article
Download all recent cumulative updates, security hotfixes, and patches listed in your Apple Updates, Windows Updates, or iOS version updates. This goes whether you have Intel, AMD, ARM, or iOS devices. You should do this as soon as humanly possible; especially if you like to Torrent or use streaming services, or online gaming or gambling sites. Don’t wait, do it right meow. If you run a WordPress site which uses 3rd party plugins or services, patch that, too.
The impact to you will be a marginal hit on your CPU loads if you’re using a computer that’s fairly recent. If you’re running an eight-year old (or older) frankenbeast computer or older generation Intel-based Apple product, I’m sorry, it’s likely gonna suck. You can expect latency hits up to 30% or more depending on processor and motherboard. Time to upgrade.
Better that than someone scraping your CPU’s unprotected dump cache for information like your billing address, credit card info, saved credentials, etc.
How these exploits work: the TL;DR
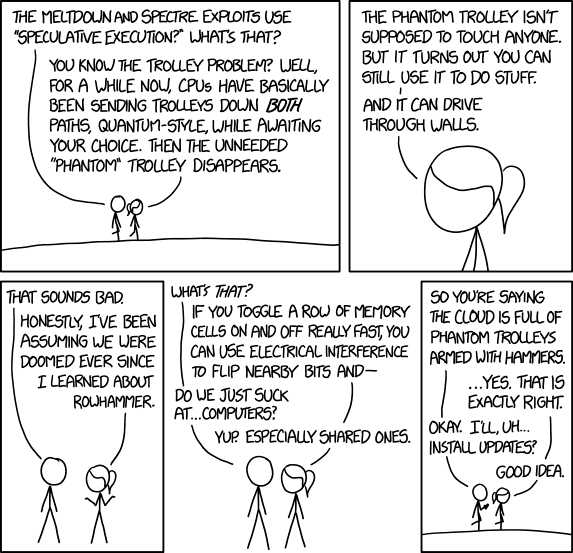
If you want a video version of the breakdown, no one gives a better breakdown than Leo Laporte and the team at This Week in Tech. His Layman’s Explanation of the vulnerability should get you up to speed, though he makes an erroneous reference to The Trolley Problem, which deals with ethics, while the issue at hand is actually how computer hardware is able to ‘guess’ what you’re likely to do based on past frequent actions in order to get that work done more quickly – a mechanic known of as Speculative Execution. This is what Spectre exploits, and ARM, AMD, and Intel are vulnerable to this.
Meltdown targets your entire physical memory (protected and user memory) and uses out-of-order instructions exploits to make all of the memory available to an attacker. Basically, it ignores the “barriers” between the memory users have access to, and the memory segments which are reserved for system and process use, to which users don’t normally have access. Protected memory is a segment of the available memory your CPU uses to manage all of its routine actions, and this space may contain anything from algorithms used to weight processing effort for programs to root-level service passwords.
The Long Version
Spectre: Speculative Execution means that your computer always operates on the two closest guesses to what the user’s (or a program, or a shared resource, or a service account, or a program’s… etc) next action will be. The processor preloads two or more routine actions, on a super-fast scale, and whichever are chosen get kept and committed to resources while the others gets dropped into dump cache. By always predicting and loading the next most likely actions, it takes less time to put these into effect when it comes time to complete processing. Until the tasks are committed, both – or many – actions are simultaneously active.
Back in the days of mainframes and computers that took up whole rooms, this made a lot of sense. Computers at that time were slow, ponderous, and storage was hella expensive. You wanted to speed things up, but only commit to memory what you were actually going to use. Everything was kept local within machines that had to be physically accessed, and there was no expectation that anyone would want to go combing through the discarded processes and actions found in the dump cache. Those were, after all, discarded data.
The problem these days is that no one ever bothered to secure that dump cache, and anyone with the skill and knowledge, and a little ingenuity, can scrape that cache to reveal information which has recently been discarded to it. The more sophisticated and automated your daily use of your computer is, the greater the risk that sensitive information will be revealed. There is further risk as well that more sophisticated means of exploiting these vulnerabilities mean someone running a website with a hidden JavaScript tool can download anything in your computer’s active memory – albeit very slowly – which is what makes sites with long session duration (like streaming sites) such a risk.
Due to the increasingly integrated nature of system architecture, and the unprotected status of the dump cache (read: there is zero hardware protection against read of this segment of cache), and because these attacks happen at the CPU level, there is a very sizable risk posed to organizations which truck in sensitive information. Due to the long times required to scrape this data, my assessment is that Spectre is – by itself – not as scary as Meltdown.
Meltdown: Meltdown works by using out-of-order instructions to essentially “trick” or bypass computer separations in memory to make all of the contents of physical memory accessible to an attacker. It’s the “hammers” in the above comic panel example, it breaks down the walls between protected and non-protected memory to make all of this available to scraping, and this is more than a little scary because it can allow attackers to gain unprotected read of system credentials, stored passwords, details of service accounts, encryption keys, etc. Basically anything which gets processed via active memory whenever processes or programs need to run or authenticate, or whenever those are prompted and the user responds.
Memory protection became standard in CPU architecture in the 2000’s because of the risk posed by allowing processes access to memory which hasn’t been allocated to it, and memory protection is designed in such a way to prevent bugs or malware from affecting other processes. Because Meltdown smashes the barriers between protected memory and user memory, it basically sidesteps this barrier and allows the attacker to access the data being processed in this protected segment.
This means that if Meltdown is running in an environment on a monitored machine when an administrator is prompted for their admin credentials, those credentials can be scooped as easily as if the computer was affected by a keylogger – a program designed to pull the input from the keyboard as it’s typed in. At which point, the attacker then has the ability to exercise the same access as the admin, or more covertly using the credentials and system passwords reserved for service accounts and root-level processes (which are passed automatically by the system to facilitate automation and daily function – like your body’s autonomic nervous system), and may gain superuser access to an un-patched machine or network.
The Implications: While exploits like this are probably the NSA’s giddy-as-a-schoolboy wet dream scenario – because you can target these attacks if you know the hostname or address information of the target device, including cellular devices dependent on ARM or Apple mobile architecture – this poses a threat to them, as well.
If you want the verbose explanation, you can see a video savvy technical here (1), here (2), here (3), and here (4). Or you can read the verbose written technical explanations here (includes whitepapers), here, or here.
These exploits, left un-patched would allow savvy and well-armed hackers to scrape data from the NSA’s application and file servers for programs like Boundless Informant, XKeyscore, and other PRISM-related programs, which hitherto would grant them access to your data as well, even without accessing your computer specifically. I mean, why scrape Joe Suburb’s machine when you can scrape Joe America’s?
The same goes if you consider the data kept and routinely processed by credit agencies like TransUnion and Equifax; healthcare providers like United Health or Johnson & Johnson; pharma companies like Phizer and Novartis; engineering companies like Amec Global and GE Energy and General Motors; and finance companies like Goldman Sachs and Berkshire Hathaway. Not to mention banks, government registries, insurance companies, and so on. There’s a reason this is in the news, and it’s because this is possibly the most significant vulnerability uncovered to date. That this vulnerability has existed for at least twenty years (conservatively) is saying something.
So what kind of data can be scraped from dump cache and active memory through leveraging these exploits? Let’s get specific with a few examples:
- Best case scenario: Attacker learns you spend too much time on ICanHasCheezburger looking at cat memes, trolling the forums of 4chan, and shitposting on Reddit.
- Best case scenario: Attacker learns you’ve used the password you created when you were twelve for all your accounts, including your porn and banking info.
- Best case scenario: Attacker learns you’re secretly a Brony furry.
- Worst case scenario: Attackers gain access to root-level process information and instructions in a Nuclear plant.
- Worst case scenario: Attackers gain access to genetic data stored by medical agencies or the Centres for Disease Control and use it for the development of targeted chemical weapons.
- Worst case scenario: Attackers gain access to air traffic control or defense systems.
Is the sky falling?
Short answer: No. Any companies, corporations, organizations, governments, developers, etc who would be at serious risk of these threats already have network security sophisticated enough to protect their physical environments; and realistically, anyone sophisticated enough to gain access to those super-secure environments already has access. At a certain level of sophistication and skill, black hats go where they want.
You can expect that if these vulnerabilities haven’t already been patched-out, they will be by end of day today (Tuesday, January 9, 2018). Most serious organizations had their teams inserting layers of protection against these exploits within an hour or two of news breaking. Any organization which doesn’t have these patched out by end of week is putting itself in danger’s path.
To protect against phyiscal (local) access to environments to exploit these vulnerabilities, almost every organization of note to whom these vulnerabilities pose significant threat have extensive (usually armed) security teams, surveillance, and air-gap distance systems to protect their really sensitive data. Further, in most countries where the payoff could even be possibly perceived as worth it to criminals and rogue elements, they face federal sentencing up to and potentially including capital punishment. So that’s a pretty big deterrent.
However, as these vulnerabilities have existed for greater than two decades, it’s anyone’s guess what’s already been leveraged by their use.